Amazon Redshift catalogs #
Use a Redshift catalog to configure access to an Amazon Redshift data warehouse.
Your Amazon Redshift cluster must meet the following requirements:
-
The cluster must be configured to be Publicly accessible (except when using AWS PrivateLink). This setting is available in the AWS console for your cluster in Properties > Network and security settings.
-
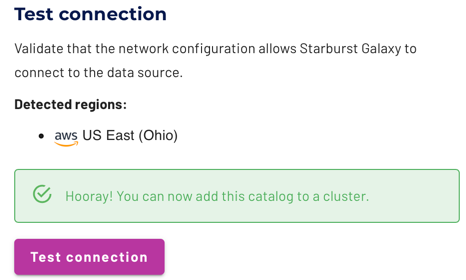
The cluster’s VPC security group is configured to allow Starburst Galaxy access. The specific range and CIDR block depends on your AWS region, as shown on the IP allowlist page. Your Redshift cluster’s region is displayed as part of the Test connection success message. Add the appropriate Starburst Galaxy IP range for your region as an inbound rule to allow the range.
Create a catalog #
Follow these steps to create a catalog for Redshift:
- In the navigation menu, select Data, then Catalogs.
- Click Create catalog.
- On the Create a catalog pane, click the Redshift icon.
- Configure the catalog as prompted in the dialog.
- Test the connection.
- Connect the catalog.
- Set any required permissions.
- Add the new catalog to a cluster.
The following sections provide more detail for creating Redshift catalog connections.
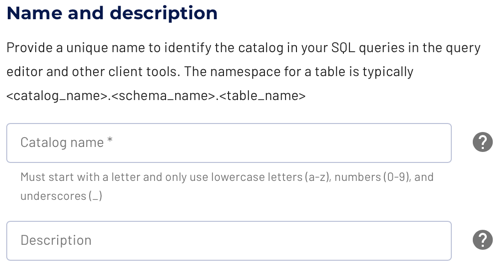
Define catalog name and description #
The Catalog name is visible in the query editor and other clients. It is used to identify the catalog when writing SQL or showing the catalog and its nested schemas and tables in client applications.
The name is displayed in the query editor, and in the output of a SHOW
CATALOGS command.
It is used to fully qualify the name of any table in SQL queries following the
catalogname.schemaname.tablename syntax. For example, you can run the
following query in the sample cluster without first setting the catalog or
schema context: SELECT * FROM tpch.sf1.nation;.
The Description is a short, optional paragraph that provides further details about the catalog. It appears in the Starburst Galaxy user interface and can help other users determine what data can be accessed with the catalog.
Multiple connections #
The Redshift catalog can only access a single Redshift database within a single catalog. If you have multiple Redshift databases, or want to connect to multiple Redshift instances, you must configure additional instances of the Redshift catalog.
Configure the connection #
Read further to learn about each supported connection method. The following sections detail the setup for the supported cloud providers.
-
Connect directly
The connection to the database requires a username, password authentication, and the details necessary to connect to the database server, typically hostname or IP address and port. -
Connect via SSH tunnel
A connection to the database can be established directly, if the Starburst Galaxy IP range/CIDR is allowed to connect.If the database is only accessible inside the virtual private cloud (VPC) of the cloud provider, you can use an SSH tunnel with a bastion host in the VPC.
-
Connect privately
Starburst Galaxy supports secure connections through AWS PrivateLink for Redshift catalogs.
Amazon Redshift on AWS #
Configure the connection information for your Redshift cluster.
Connection types #
Starburst Galaxy supports three connection types for Amazon Redshift:
- Direct connection
-
Provide your cluster’s Redshift endpoint. Locate the Endpoint value in the General information tab of the AWS console for your Redshift cluster. This is typically the fully qualified domain name for your Redshift cluster in the form
host:port/databaselike the following example:clustername.random.region.redshift.amazonaws.com:5349/databasename - SSH Tunnel
-
Provide your cluster’s Redshift endpoint.
-
Select the appropriate SSH tunnel name from the drop-down list. See SSH tunnel to learn about adding names to this list.
- AWS PrivateLink
-
Select the appropriate PrivateLink name from the drop-down list. See AWS PrivateLink to learn about adding names to this list.
Authentication methods #
Starburst Galaxy supports a number of authentication methods for Amazon Redshift:
- Password based
-
For this method, specify database username and database password. Specify a username with sufficient access rights to allow the desired querying.
- AWS access key
-
For this method:
- From the drop-down list, select the AWS region that contains your Redshift cluster.
- Specify the database username.
- Specify the AWS access key and AWS secret key. See AWS access and secret key to learn how to configure these keys for your AWS account. Your browser might try to fill the two key fields with your browser login name and password. If so, overwrite these fields with the correct values.
- AWS IAM role
-
For this method:
- From the drop-down list, select the Redshift region that contains your Redshift cluster.
- Specify the Database username.
- From the drop-down list, select the Cross account IAM role. See Cross account IAM role to learn how to configure an AWS cross account IAM role for your AWS account.
Test the connection #
Once you have configured the connection details, click Test connection to confirm data access is working. If the test is successful, you can then save the catalog.
If the test fails, look over your entries in the configuration fields, correct any errors, and try again. If the test continues to fail, Galaxy provides diagnostic information that you can use to fix the data source configuration in the cloud provider system.
Connect catalog #
Click Connect catalog, and proceed to set permissions where you can grant access to certain roles.
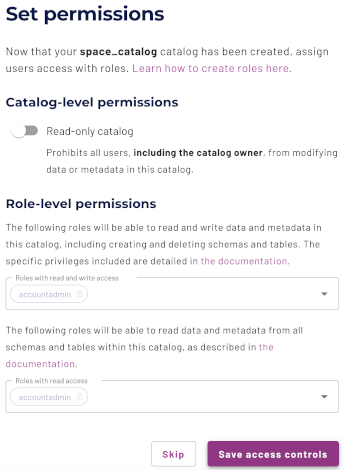
Set permissions #
This optional step allows you to configure read-only access or full read and write access to the catalog.
Use the following steps to assign read-only access to all roles:
- Select the Read-only catalog switch to grant a set of roles read-only access to the catalog’s schemas, tables, and views.
- Next, use the drop-down menu in the Role-level permissions section to specify the roles that have read-only access.
- Click Save access controls.
You can specify read-only access and read-write access separately for different sets of roles. That is, one set of roles can get full read and write access to all schemas, tables, and views in the catalog, while another set of roles gets read-only access.
Use the following steps to assign read/write access to some or all roles:
- Leave the Read-only catalog switch cleared.
- In the Role-level permissions section:
- Expand the drop-down menu in the Roles with read and write access field and select one or more roles to grant read and write access to.
- Expand the drop-down menu in the Roles with read access field and select one or more roles from the list to grant read-only access to.
- Click Save access controls.
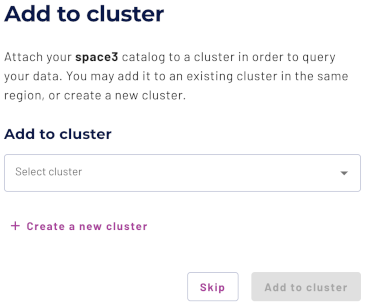
Add to cluster #
You can add your catalog to a cluster later by editing a cluster. Click Skip to proceed to the catalogs page.
Use the following steps to add your catalog to an existing cluster or create a new cluster in the same cloud region:
- In the Add to cluster section, expand the menu in the Select cluster field.
- Select one or more existing clusters from the drop down menu.
- Click Create a new cluster to create a new cluster in the same region, and add it to the cluster selection menu.
-
Click Add to cluster to view your new catalog’s configuration.
SQL support #
The catalog provides read access and write access to data and metadata in Redshift. It supports the following features:
- Globally available statements
- Read operations
- Write operations
- Data management:
- Schema and table management
The following sections provide Redshift catalog-specific information regarding SQL support.
Data management details #
If a WHERE clause is specified, the DELETE operation only works if the
predicate in the clause can be fully pushed down to the data source.
Schema and table management details #
The catalog does not support renaming tables across multiple schemas. For example, the following statement is supported:
ALTER TABLE catalog.schema_one.table_one RENAME TO catalog.schema_one.table_two
The following statement attempts to rename a table across schemas, and therefore is not supported:
ALTER TABLE catalog.schema_one.table_one RENAME TO catalog.schema_two.table_two
The catalog supports renaming a schema with the ALTER SCHEMA RENAME
statement. ALTER SCHEMA SET AUTHORIZATION is not supported.
Is the information on this page helpful?
Yes
No
